Ticker: $ALK
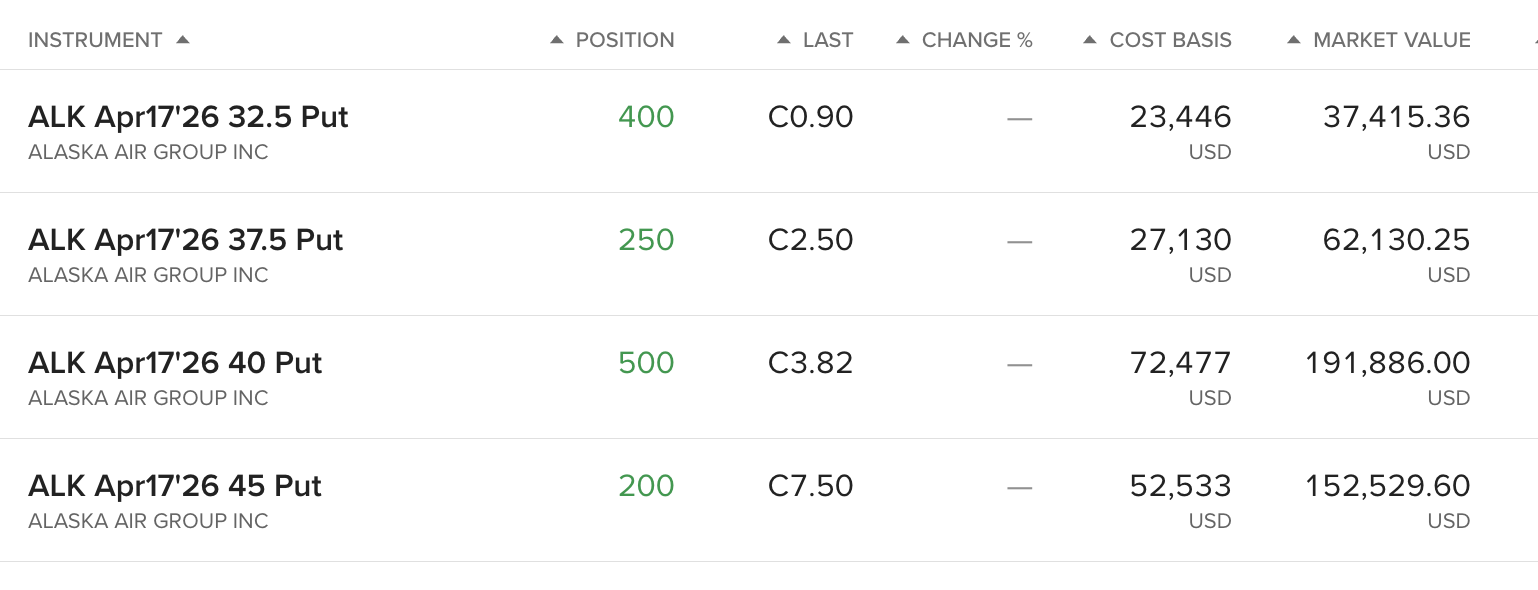
Positions (proof: https://imgur.com/sgHeFzw):
- 400x ALK Apr 17 2026 $32.50 Puts @ $0.59 Current $0.90
- 250x ALK Apr 17 2026 $37.50 Puts @ $1.09 Current $2.50
- 500x ALK Apr 17 2026 $40.00 Puts @ $1.45 Current $3.82
- 200x ALK Apr 17 2026 $45.00 Puts @ $2.63 Current $7.50
Total value at risk: ~$440k
Shouted about this before.
If you'd listened then you'd be well in the money. Nothing to do with Iran – trust me bro.
Since then I haven't sat still. I've found lots more mischief:
I Found Some Sellers
Six different ones. Deep in the Dark Web? only if that is what we are calling Facebook these days – just a basic search.
One of them claims selling 60 Alaska accounts a week.
They show off similar pricing: $120 for 220k miles. That is enough miles for 4 peeps on flats bed across the Atlantic.
I Followed the Money
Sellers offer up crypto wallets. Follow this one yourself:
0xA7964B5b406f439Dd527eAB89604e437E968D827
Goes all the way to 100s of millions heading into Binance.
An organised crime racket.
I Found The Reason for the PIN Lock
Victims get forced into using a verbal PIN after they have been hacked. Why?
Password changes don't do anything if a villain is in your account.
Try it yourself:
- Log into Alaska in two different browsers.
- Change your password in one of them.
- Refresh the page in the other.
- Observe you are still fully logged in on browser 2.
You can keep that rogue session alive for a long time.
I Found Out Hackers Don't Need Passwords
Session cookies are wide open at they don't have HTMLOnly.
Obviously you don't know what that means, but any rogue chrome extension, or any rogue cookie in the system, means they skip the password bit and are in an account any time they like.
I Found Plenty More Junk
But this is enough to know the loyalty programme valued at $12 billion on a market cap of $4.5 billion is not locked down.
The Play
Probably go longer dated that I am. Puts FTW.
Positions (proof: https://imgur.com/sgHeFzw):
- 400x ALK Apr 17 2026 $32.50 Puts @ $0.59 Current $0.90
- 250x ALK Apr 17 2026 $37.50 Puts @ $1.09 Current $2.50
- 500x ALK Apr 17 2026 $40.00 Puts @ $1.45 Current $3.82
- 200x ALK Apr 17 2026 $45.00 Puts @ $2.63 Current $7.50
Total value at risk: ~$440k
ETA: Full analysis here.
DD: Alaska Airlines ($ALK) – Puts on 4 year cyber leak left unpatched
byu/NorthcoteTrevelyan inwallstreetbets
Posted by NorthcoteTrevelyan

18 Comments
damn you really went full investigative journalist on this one 💀 following crypto wallets and testing session cookies like you’re running your own cybersecurity firm 😂
how much money do they lose really, wouldn’t this just increase seat utilization until they decide to patch it. The seats are basically free to them thats how this whole miles thing works
4 year old vulnerability but you have short dated puts? What makes you think the bottom is going to fall out in that time period?
This might not get the amount of interaction and love as it deserves.
But we appreciate this kind of autistic DD. This is awesome
Hmm the issue I see with this is that the company itself is not breached. The accounts may have been taken over, but sessions are not infinite post password reset. What can the attacker take of value? Miles? That’s not enough to result in a 5-10% drop of the company value. It might have some impact, but again the company’s database is not breached there is no evidence of that.
Session hijacking exists everywhere btw. This isn’t unique to Alaskan Airlines… for example Targets database was exfiled, millions of credit cards stolen and the CEO resigned. There are Google accounts being stolen everyday, I don’t think Google is gonna take a hit some time soon.
Also a major breach shouldn’t take months to have some kind of brand impact.
love this, thanks
You vastly underestimate how many people will participate in the fraud, and actually buy, then try to use these points.
Petty sure you need a valid license to fly, and that there would be some sort of a paper trail for the buyer that used the points. And you think the average Facebook point purchaser is going to know how to use points for someone else’s account?
This is a nothingburger if I’ve ever seen one.
Spicy AF. More of this!
Autistic-Level: 12/10.
There’s no correlation between the hack and the stock price, and absolutely no causation. In summary: a classic WSB DD.
No one (really) cares about such data leaks.
There have been many breaches on big corporations and hardly did it ever have any mid or long term effect.
The flaw appears to be in their website. Looks like the individual customer still needs to be hacked. Just an FYI, but a lot of companies pay bug bounties for this kind of thing. You might want to look into that. They might actually pay you for that information.
As a cyberprofessional, I appreciate this kind of deep dive. I would add, this isn’t the type of security flaw that tanks a company. We aren’t talking ransomware here or mass data exfiltration.
Side note, attackers don’t guess passwords, they steal them. Once they have access to a device, it’s pretty much game over. In this particular case, it’s the device of customers that use Alaska. It’s a nice gig for them, but you aren’t talking about the ability to extort millions from the airline.
It’s a damn shame this god-tier DD will get buried under 500 low-effort NVDA meme posts. This is exactly what this sub was built on.
I doubled my money on some $50 6/18 puts based on your earlier post. 🤷♂️
[You again?](https://old.reddit.com/r/wallstreetbets/comments/1qcozu0/dd_alaska_airlines_alk_long_dated_puts_on/)
https://preview.redd.it/g7znjgo297qg1.png?width=399&format=png&auto=webp&s=a1b49fcc97a01fd74bd3d56bfea166381f6f81e7
Goes deep. The polar bears might be involved. Bought.
i mean, yeah, the stock is down, but allow me to vaguely gesture to what’s going on outside to be the most likely reason for the nose dive in price KEKW
If this was real you’d have made more money via the bounty program. As is, this is a nothing burger.
The session might remain, but try to take action on something and the server will verify the token is no longer working.